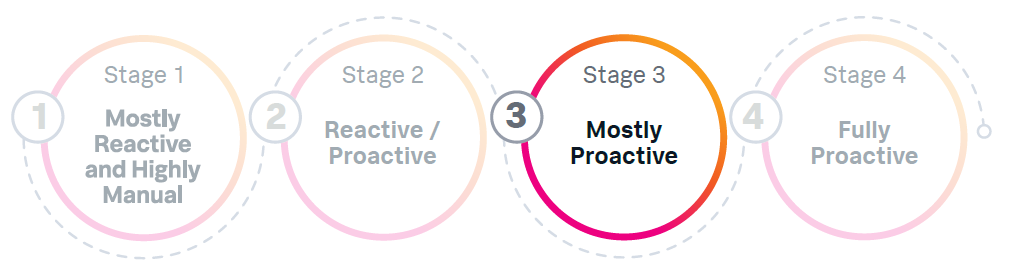
Stage 3 of the SOAR Adoption Maturity Model
Characteristics of an organization in the Mostly Proactive stage
At stage 3, the organization has mature SOC procedures and processes. Evaluates threats with triage and investigation capabilities and/or has outsourced capability for deep forensics. At various levels of team formation for security engineering, threat hunting, forensic/malware analysis, threat intelligence and more. The team is starting to leverage metrics for operational improvement and uses standard incident response methodologies. Conducts a lessons learned analysis.
The SOC at this stage might be described as centralized SOC, federated SOC, or managed SOC. The CISO has a capable security team with a security architect who runs engineering and a SOC manager who has standardized security practices with documented processes and some automation. The CISO has hired an incident response team manager to build out a computer security incident response team (CSIRT) with forensics, threat hunting, intelligence, and purple team capabilities. The CISO wants to source L2 and has all L3 in-house or might create a larger L3/CSIRT team and smaller SOC team.
How to advance past this stage
The end goal of stage three is to use advanced playbooks to customize your environment. The value of this stage is better customization and consistent automation of advanced workflows, such as the following:
- Deploying countermeasures
- Advanced investigations with forensic data
- More surgical response capabilities
- Reverse malware engineering
- Automatic email search and purge
Common use cases
- Splunk notable enrichment
- Critical investigation review
- Ticketing system integration
- Email investigation
- External alert enrichment
For more Splunk SOAR use cases, see the Security Use Case Library.
Common SOAR applications
- Splunk App for SOAR Export
- SOAR HTTP app
- Splunk App for SOAR
- Ticketing apps
- Reputation/intelligence
- Email apps
- Endpoint apps
- Identity apps
- Cloud apps
For more information on Splunk SOAR Connectors and to engage with the developers, see the GitHub repository.
Common SOAR playbooks
- Input playbooks for above apps
- Risk alert auto containment playbooks
- aws_disable_user_accounts
- block_indicators
- c2_investigate_and_contain
- compromised_email_containment
- crowdstrike_malware_triage
- customer_firewall_request_handle_artifact
- domain_block_umbrella
- ec2_instance_isolation
- host_quarantine_crowdstrike
- lost_device_response
- malicious_insider_containment
- protectwise_investigate_and_respond
- ransomware_investigate_and_contain
- risk_notable_auto_containment
- risk_notable_block_indicators
- risk_notable_protect_assets_and_users
- vmworld_c2_response
- vmworld_wannacry_response
- wannacry_remediate
- zscaler_hunt_and_block_url
- zscaler_malicious_file_response
- Process termination
- File removal
- Reverse malware analysis
- Dynamic observable analysis
- Advanced content formatting
- Dynamic customer interaction
- Threat intelligence automation
- dns_hijack_enrichment
- Identifier_Activity_Analysis_Dispatch
- intelligence_management_enrich_indicators
- recorded_future_correlation_response
- recorded_future_handle_leaked_credentials
- recorded_future_indicator_enrichment
- recorded_future_threat_hunting
- risk_notable_review_indicators
- symantec_ioc_data_enhancement
- threatquotient_investigate_and_respond
- threat_intel_investigate
- trustar_network_enrichment
- wannacry_hunting
- Vulnerability management processes
For more Splunk SOAR playbooks, see the GitHub repository.