Sending Splunk Observability events as Workflow Actions from Splunk SOAR
It can be helpful for Splunk Observability Cloud users to be notified of automation and remediation being run in Splunk SOAR, even if they don't have access to use Splunk SOAR. You can use a Splunk SOAR app to send those users a notification. For example, you can send your developers a notification of a vulnerability being remediated in the development team’s container deployment.
This is only one example use case. You can apply this use case to any data within your Splunk deployment and any actions or playbooks used in Splunk SOAR.
Solution
- In the Apps section of your Splunk SOAR installation, search for the SignalFx app.
.png?revision=1)
- Configure the app. You will need to enter:
- Your SignalFx (Splunk Observability Cloud) API URL (e.g. https://api.us0.signalfx.com)
- Your Splunk Observability Cloud API Access Token
.png?revision=1)
- Add a new action to your playbook or create a new playbook.
- Add in the SignalFx Create Observability Event action and configure your inputs:
- Title. The title of your event that you will match on in Splunk Observability Cloud.
- Dimensions. This is a JSON payload defining the dimensions you want to send with your event. In the example below the datapath is added for "artifact.*.hash", a static declaration for “repository” of “frontend”, and a datapath for "container.name".
.png?revision=1)
For details about creating your dimensions payload, check the documentation for the SignalFx SOAR App.
- Run your playbook and action, either manually or as part of an automated playbook workflow in Splunk SOAR to send the event to Splunk Observability Cloud.
- In your Splunk Observability Cloud dashboard, choose an Event Overlay to match your event name. You can use an asterisk * as a wildcard.
.png?revision=1)
- In your chart, enable Show events as lines and Show data markers for overlaying events on that chart.
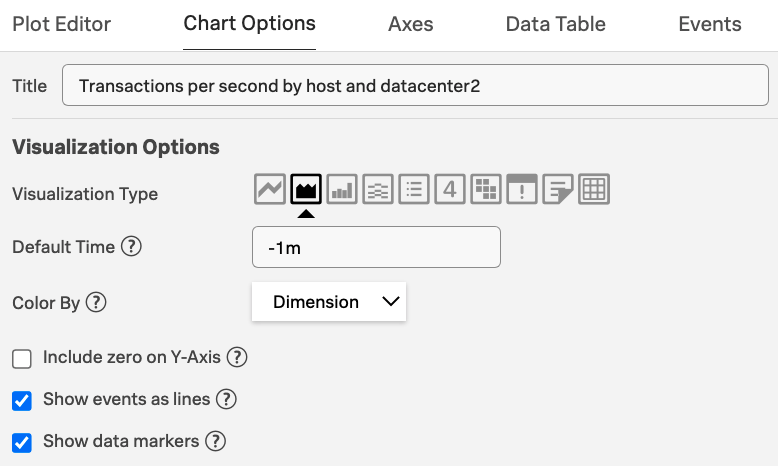.png?revision=1)
Events will now be overlaid on your chart.
.png?revision=1)
Next steps
This resource might help you understand and implement this guidance:

