Getting started with SOAR
To make the most of your investment in Splunk SOAR, it’s important that you understand some core concepts and the value that security orchestration, automation and response solutions can bring to your team.
What is Splunk SOAR?
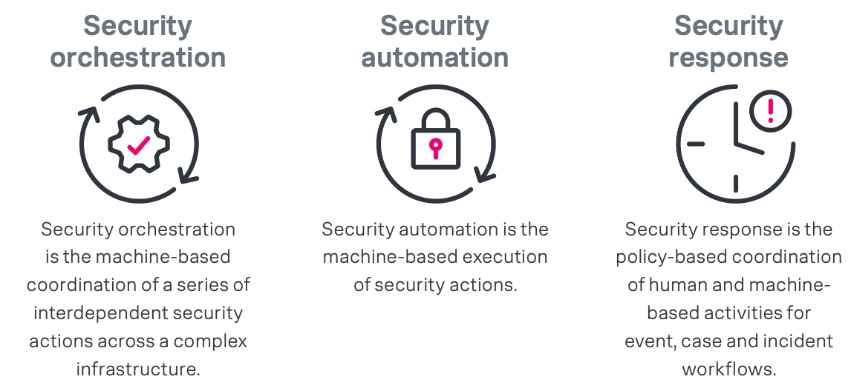
Splunk SOAR is a Security Orchestration, Automation, and Response Solution. Here is a quick explanation of each major facet of a SOAR solution:
What problems does Splunk SOAR help solve?
Splunk SOAR helps you operationalize security, so you can work smarter, respond faster, and strengthen your overall security posture.
SOAR centralizes capabilities such as case and incident management features, threat intelligence management, essential state of operations dashboards, reporting, and analytics that can be applied across various functions throughout the incident lifecycle. SOAR empowers the SOC by using technology and processes to help human analysts address alerts, which in turn reduces risk.
What are some business initiatives that Splunk SOAR ties into?
- Automating repetitive tasks
- Triaging security incidents faster with automated detection, investigation, and response
- Strengthening your defenses by connecting and coordinating complex workflows across your team and tools
What does adoption of SOAR look like?
Splunk SOAR is all about increasing your overall productivity and empowering your security team to work smarter, not harder, via the power of automation. For you to adopt this product and gain the most value, you must provide access to data from SIEMs or tools like email applications via Splunk SOAR’s API.
Splunk SOAR offers an extensible interface for integration with over 350 apps and 2,150 actions. You can also customize apps to better solve your problems. To further increase security actions speed during the process, you can set up pre-made playbooks or create your own playbooks by using visual playbook editors, which are built into Splunk SOAR.
To get started, review the Splunk SOAR Adoption Maturity Model to determine what stage of security orchestration, automation, and response your organization is at. By understanding where your organization is within the different phases of the maturity curve, you’ll be able to identify the use cases, playbooks, and workflows most relevant to your security needs. This will provide a better understanding of your security roadmap, and — better yet — how to reap the rewards of SOAR.
Additional resources
- Slack: #soar on the Splunk Community Slack (sign up here)
- Splunk Answers: SOAR discussion area
- Splunk blogs: Supercharge your SOC investigations with Splunk SOAR 6.4
- Quick reference: SOAR quick reference guide

