Checking for files created on a system
You are a security analyst looking to improve threat detection on your endpoints. You already use Sysmon, particularly event code 1 - process creation, to gain fidelity into programs starting on your systems, but you know there are other Sysmon events that you might want to use during your hunts. You're especially interested in digging more into situations where files have been created on a system, which could complement your existing hunt techniques and potentially also help you drive more automation.
Data required
Microsoft: Sysmon
Configuration needs to be performed to get the most out of your Sysmon events. You can access templates to help you get started, for example the Swift on Security configuration.
How to use Splunk software for this use case
Run the following search. You can optimize it by specifying an index and adjusting the time range.
source="xmlwineventlog:microsoft-windows-sysmon/operational" EventCode=11 host=<hostname> process_name=<processname> | table file_create_time file_path process_name host | sort _time
Search explanation
| Splunk Search | Explanation |
|---|---|
source="xmlwineventlog:microsoft-windows-sysmon/operational" |
Search only for Sysmon operational data. |
EventCode=11 |
Search for event code 11, files created on a system. |
host=<hostname> |
Search on a host you specify. |
process_name=<processname> |
Search for a process name you specify. |
|
|
Display the results in a table with columns in the order shown, sorted by time. |
Next steps
Here is an example result, showing host ghoppy-1 running a process called setup.exe, with the resulting files created and their associated paths:
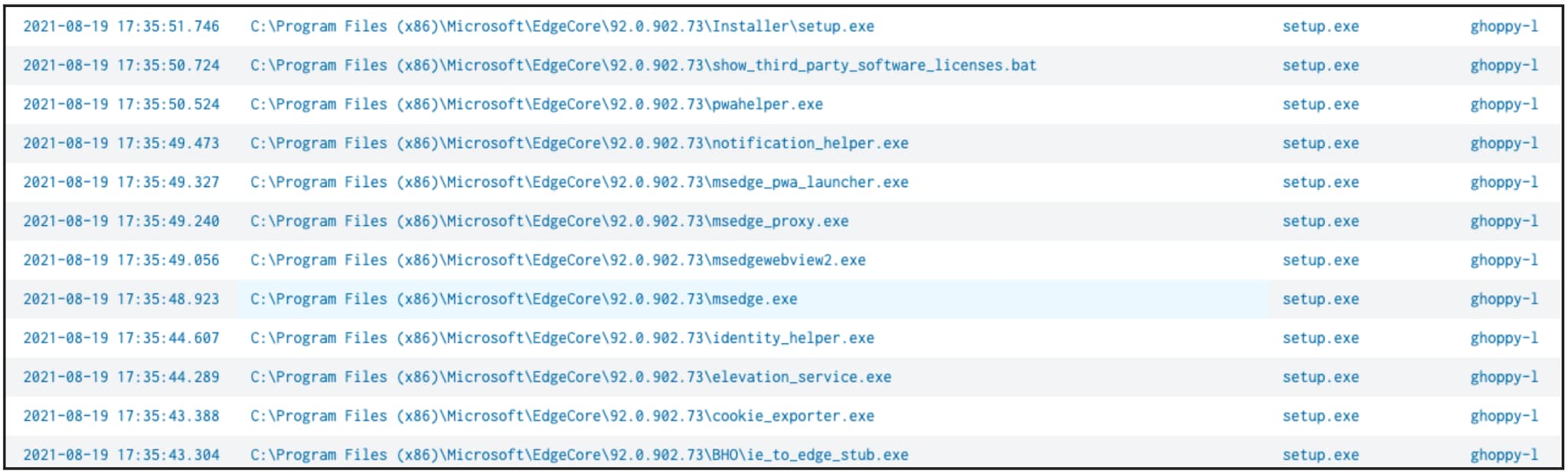
This event code can return an excessive number of false positives, depending on which directories and file types it monitors, so you'll need to investigate further to exclude benign results.
The content in this guide comes from a previously published blog, one of the thousands of Splunk resources available to help users succeed. In addition, these Splunk resources might help you understand and implement this use case:
- Splunk Lantern Article: Visualizing processes and their parent/child relationships
- Splunk Lantern Article: Monitoring a network for DNS exfiltration
- Splunk Blog: Process hunting with a process

