Monitoring DNS queries
You are a security analyst looking to improve threat detection on your endpoints. You already use Sysmon, particularly event code 1, process creation, to gain fidelity into programs starting on your systems, but you know there are other Sysmon events that you may want to utilize during your hunts. You're especially interested in digging more into the detail of DNS queries, which could complement your existing hunt techniques and potentially also help you drive more automation.
Data required
Configuration needs to be performed to get the most out of your Sysmon events. You can access templates to help you get started, for example the Swift on Security configuration. You'll also need to install the Splunk Add-On for Microsoft Sysmon.
How to use Splunk software for this use case
Run the following search. You can optimize it by specifying an index and adjusting the time range.
source="xmlwineventlog:microsoft-windows-sysmon/operational" EventCode=22 EventDescription="DNS Query" host="<hostname>" Image="[C:\\Program Files(x86)\\Microsoft\\Edge\\Application\\msedge.exe]" QueryName="<URL>"
Explanation
| Splunk Search | Explanation |
|---|---|
source="xmlwineventlog:microsoft-windows-sysmon/operational" |
Search only Sysmon operational data. |
EventCode=22 EventDescription="DNS Query" |
Search for event code 22, DNS queries being executed by a specific path on a specific host. |
QueryName="<URL>" |
Search for the URL specified. |
Next steps
Here is an example result, showing host bstoll-1 using Microsoft Edge to look up www.blogger.com and getting an IP address back in response:
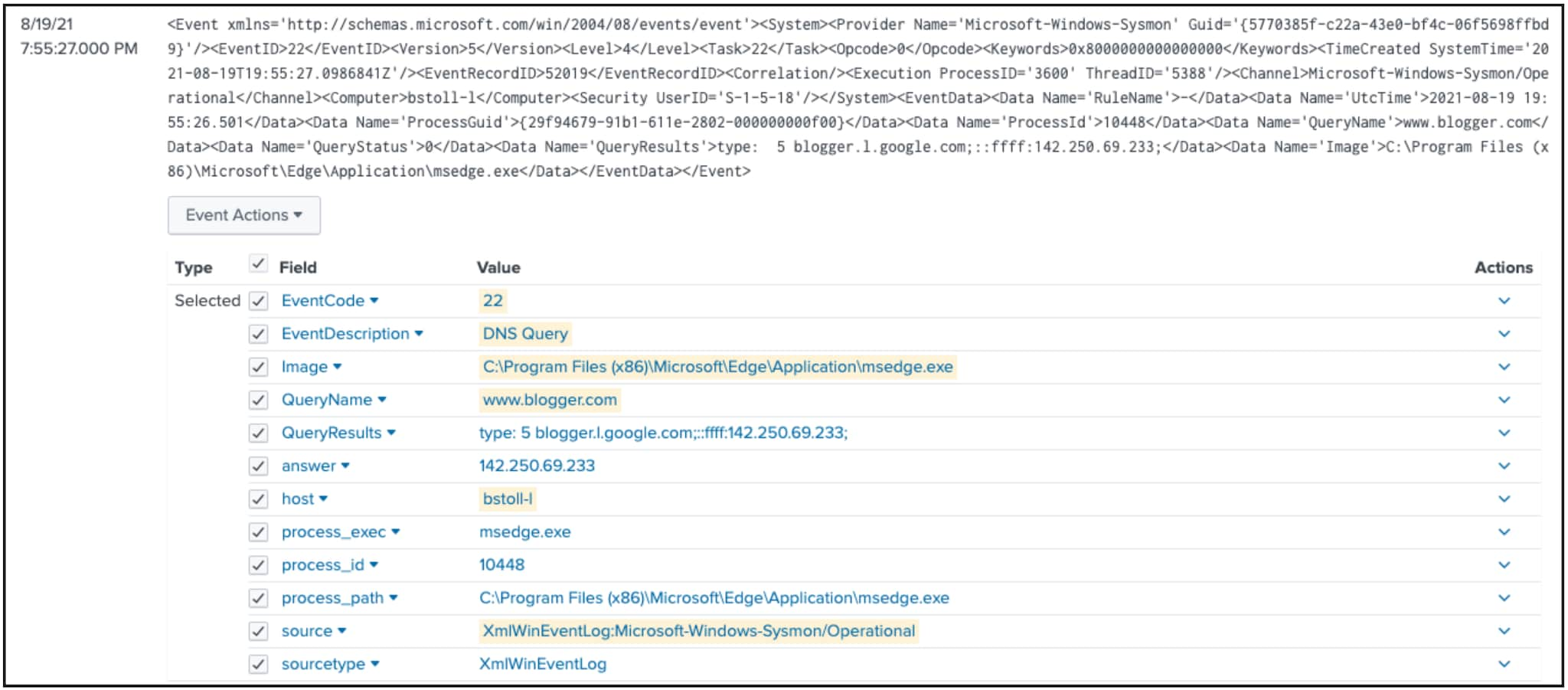
In this example, the result is benign, but this search could return both benign and suspicious results. Modifying the image on a suspect host could yield greater insight on domain queries.
The content in this guide comes from a previously published blog, one of the thousands of Splunk resources available to help users succeed. In addition, these Splunk resources might help you understand and implement this use case:
- Splunk Lantern Article: Visualizing processes and their parent/child relationships
- Splunk Lantern Article: Monitoring a network for DNS exfiltration
- Splunk Blog: Process hunting with a process

